AWS AgentCore Payments gives AI agents a wallet
Amazon Bedrock AgentCore Payments previews a runtime layer where AI agents can pay for APIs, MCP servers, web content, and other agents with x402.

- What happened: AWS previewed
Amazon Bedrock AgentCore Payments.- It lets agents pay for paid APIs, MCP servers, web content, and other agents through Coinbase or Stripe wallet infrastructure.
- Why it matters: Payment is moving from checkout screens into the agent execution loop.
- HTTP 402,
x402, theX-PAYMENTheader, session budgets, and observability now sit in one runtime control plane.
- HTTP 402,
- Watch: A payment agent failure is not just a bad answer. It can become real spend.
- A May 12, 2026 x402 security paper flags authorization, binding, and replay-protection attack surfaces.
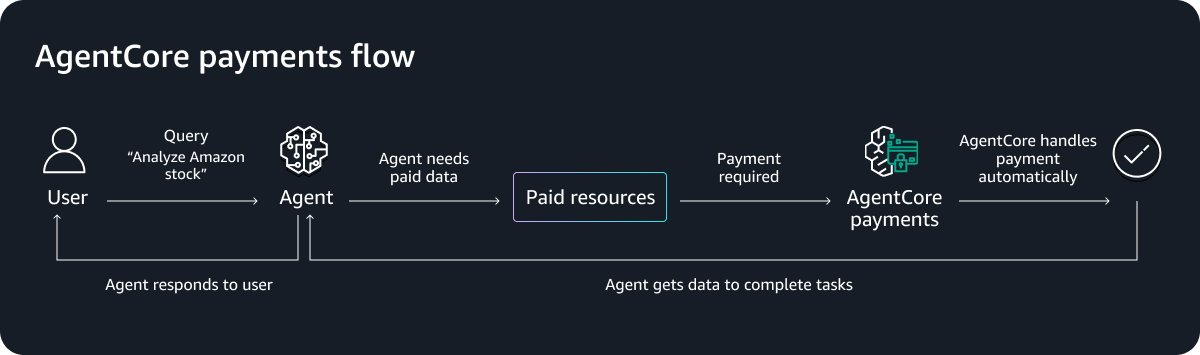
On May 7, 2026, AWS announced a preview of Amazon Bedrock AgentCore Payments. The name is long, but the product idea is direct: when an AI agent encounters a paid API, MCP server, web resource, or another paid agent during execution, it can make the payment inside a user-approved wallet and budget.
This is easy to misread as a small payment feature attached to Bedrock. It is more interesting than that. Until now, most agent tool calls have depended on free APIs, pre-provisioned API keys, internal company permissions, or SaaS accounts that a human had already purchased. AgentCore Payments adds a new pattern. The agent can discover that a resource is paid, inspect the price requirement, attach proof of payment, retry the request, and leave the transaction inside the same trace and metrics surface as the rest of the run.
In other words, payment is being treated less like a human checkout event and more like a tool call in the agent loop. That is why AWS brought both Coinbase and Stripe into the launch. This is not just an AWS billing option. It is an attempt to define how agents spend money on internet resources from inside a managed runtime.
Why agent payments are back
The more useful agents become, the more often they hit external resource costs. A financial research agent may need real-time market data and paywalled reports. A coding agent may call a sandbox, private package registry, static analysis API, or paid MCP server. Legal, medical, and security research agents may need even more expensive data and tools.
The old billing model is clumsy for that shape of work. A person signs up for a website, enters a card, starts a monthly subscription, creates an API key, and stores it in an environment variable. A company negotiates vendor contracts, attaches a cost center, and reviews access permissions. That model is stable, but it is not dynamic. If an agent decides it needs one paid data point during a task, a full subscription and vendor onboarding flow is too heavy.
AWS frames this problem explicitly. The services and content agents use need to be designed for both humans and agents, and some resources may be charged in real time at fractions of a cent. AWS also acknowledges the risk. A misconfigured payment flow does not merely produce a bad answer. It moves real money.
That line is the heart of the product. Agent payments are not about giving an LLM a card number. They are about identifying spend events, limiting budgets, separating authorization, and leaving enough logs and traces for audit. AgentCore Payments sits beside AgentCore identity, gateway, and observability because money turns a tool call into an accountable action.
How AgentCore Payments works
In the preview, developers attach payments to an existing agent through the AgentCore SDK or console. The payment connector can use a Coinbase CDP wallet or Stripe Privy wallet. A user funds a wallet and explicitly authorizes wallet access for an agent run. The session then carries controls such as maxSpendAmount, currency, and expiry time.
When the agent requests a paid resource, the first request can fail with HTTP 402 Payment Required. This is where x402 enters the system. x402 is Coinbase's HTTP-native payment protocol that gives the long-unused 402 status code a concrete payment negotiation flow. AgentCore reads the payment requirement, checks the session budget, retrieves wallet credentials, creates payment proof, and retries the original request with an X-PAYMENT header. The resource provider verifies the proof and returns the API response or content.
AWS describes the control model through PaymentManager, PaymentConnector, PaymentSession, and PaymentInstrument. PaymentManager is the configuration boundary inside an AWS account. PaymentConnector links to an external provider such as Coinbase or Stripe. Credentials are managed through AgentCore Identity and AWS Secrets Manager. PaymentSession is the payment context for a specific agent-user interaction, with budget and expiry controls. PaymentInstrument represents the user's payment method or wallet address.
The important design point is that the agent does not receive an unlimited wallet. AWS says the user must explicitly approve wallet access, runtime sessions enforce limits, and over-limit payment requests are rejected. Transactions also appear in AgentCore logs, metrics, and traces. If an agent spends money, a team needs to know not only how much it spent and where, but also which reasoning path and tool calls led to that payment.
Why HTTP 402 suddenly matters
HTTP 402 Payment Required has existed for a long time, but the web mostly routed around it. Online payment grew through accounts, cookies, card forms, subscriptions, app stores, and payment processor SDKs. For a person in a browser, that made sense.
Agents change the ergonomics. An agent is closer to an API client than a shopper in a checkout flow. If a resource costs one cent per request, the agent needs a protocol, not a checkout page. The natural loop is request, receive a price and payment requirement, sign or attach a proof, then retry.
Coinbase's x402 documentation describes this as a way to pay programmatically for APIs and content without accounts, sessions, or complex authentication. The Linux Foundation also announced the x402 Foundation on April 2, 2026, with early supporters including AWS, Coinbase, Cloudflare, Stripe, Visa, Mastercard, Google, Shopify, Circle, Solana Foundation, and KakaoPay.
That makes AWS's first-protocol choice notable. Treating x402 as the first payment protocol in AgentCore Payments is not just a crypto integration. AWS is positioning the payment negotiation as a runtime service. Developers do not have to integrate every payment protocol inside every agent application. They can push negotiation into the AgentCore layer and let the runtime enforce budgets, credentials, and audit.
Why Coinbase and Stripe are both here
The launch is also interesting because Coinbase and Stripe appear together. Coinbase provides x402 and CDP wallet infrastructure. Stripe enters through Privy wallet infrastructure as an AgentCore payment connector. AWS presents them less as direct rivals and more as the first wallet and payment rails behind the preview.
That matters because agent payments will not collapse into a simple crypto-versus-card debate. x402 fits stablecoin-based micropayments well. API calls, data fragments, report snippets, and paid agent tasks may be too small or too frequent for traditional card authorization economics. Broader commerce is different. Booking a flight, buying goods, reserving a hotel, or placing an enterprise purchase still needs fraud systems, chargebacks, compliance, and merchant policies.
AWS also says micropayments are only the starting point. The next pieces include buyer intent verification, more protocols, and end-to-end observability. An agent paying another API a few cents and an agent buying a plane ticket for a user both fall under "payments," but the safety envelope is different.
That is where this story differs from the earlier Visa Agentic Ready pattern. Visa's focus is consumer purchase flows on top of existing card networks. AWS AgentCore Payments is aimed at developer infrastructure and agent runtimes. One asks how an agent buys something on behalf of a person. The other asks how an agent buys a digital resource while working. Those paths may converge, but the first deployment surfaces are different.
| Category | AgentCore Payments | Traditional API billing | Consumer agentic commerce |
|---|---|---|---|
| Primary use case | An agent calls paid resources during execution | A developer signs a contract and uses an API key | An agent buys products or services for a user |
| Payment trigger | HTTP 402 and an x402 payment requirement | Subscription, invoice, or usage billing | Checkout, wallet, or card authorization |
| Control unit | Session budget, expiry, and trace | Account-level quotas and billing | User intent, authentication, and merchant policy |
| Main risk | Replay, binding failures, overspend, and paid-but-denied flows | Leaked keys, runaway usage, and vendor lock-in | Wrong purchases, fraud, refunds, and disputes |
Where MCP changes the market
One AWS detail is easy to skip. The Coinbase x402 Bazaar MCP server is exposed through AgentCore Gateway, and AWS says agents can discover more than 10,000 x402 endpoints. This is about discovery as much as payment.
MCP has quickly become a common interface for exposing tools and data to agents. So far, many MCP servers have been a way to expose tools an organization already owns. Adding x402 Bazaar points toward a different market. An agent could discover an external paid tool, inspect its schema and price, pay for it on the spot, and use it inside the current task.
If that model becomes real, the API economy changes. Today an API seller operates documentation, free trials, signup forms, API key issuance, billing dashboards, and sales plans. In an agent market, the API itself needs to be a machine-readable product. It needs to describe its capability, input schema, per-call price, response quality, SLA, merchant identity, and payment verification method in a way an agent runtime can understand.
This also widens the attack surface. A malicious endpoint could ask for excessive payment, impersonate a similar service, fail to deliver after payment, or leak prompt/context data through payment metadata. Discovery needs more than search ranking. It needs registry governance, reputation, allowlists, merchant identity, and spending policy.
The largest variable is security
Five days after the AgentCore Payments announcement, a paper titled Five Attacks on x402 Agentic Payment Protocol appeared on arXiv. The authors argue that x402 combines HTTP authorization with blockchain settlement and creates cross-layer attack surfaces that do not exist in the same form in conventional web payments or on-chain payments alone. They describe attacks around authorization, binding, replay protection, and web-layer handling, with possible outcomes such as unpaid service or paid-but-denied failures.
One preprint does not prove x402 is broken. It also does not audit the entire AWS AgentCore implementation. But the timing matters. In the same week AWS pushed agent payments into a managed cloud runtime, researchers publicly mapped risks in the underlying protocol family. This is the kind of feature where launch and security validation have to move together.
Paid-but-denied is especially intuitive for developers. If the agent pays and does not receive the resource, the user experiences the agent as having wasted money. Unpaid service is the seller-side mirror image. Both may look like noise at tiny amounts, but agents can repeat calls thousands of times.
Session limits and observability reduce part of the risk, but they are not the whole answer. Agent payment systems need protocol validation, nonce and replay defenses, service binding, merchant identity, price integrity, refund paths, dispute handling, and prompt/data leakage controls. The important product question is not just whether an agent can pay. It is how quickly the system can detect, block, and explain bad payments.
What builders should prepare for
AgentCore Payments will not immediately rewrite every billing model. It is a preview, regional availability is limited, and the x402 ecosystem is still early. Still, it points to several practical shifts.
First, APIs may need to be sellable to agents, not only humans. Documentation and signup flows are not enough if the buyer is a runtime. Capability metadata, machine-readable pricing, payment proof verification, and MCP-style registry exposure may become part of the product surface. For small API companies, that could be a new distribution channel: paid calls when an agent needs a specific capability, without a traditional sales process.
Second, agent cost management will move beyond tokens. Teams already track LLM tokens, vector databases, inference, and cloud runtime spend. Paid tools, paid data, and paid agents add another layer. A single agent session might spend 20 cents on model calls and $1.50 on external data. Budget policy and trace analytics become part of product operations, not just finance reporting.
Third, permissions have to become narrower. "This agent can access the internet" becomes risky once the internet can charge it. Teams will need policies for which resource categories are allowed, how much each agent can spend, which domains or MCP registries are trusted, whether recurring payments are allowed, and whether a failed response can trigger another payment retry.
Fourth, refunds and disputes need an agent-aware path. A mistaken human purchase and a mistaken agent purchase are not the same operational problem. The agent may leave a trace explaining why it acted, but whether that trace is enough for a commercial or legal dispute is a separate question. Some of this belongs in payment protocols. Some of it belongs in merchant policy.
The agent economy needs controls first
"Agentic economy" can sound inflated, and many pieces are still immature. Most APIs do not support x402. Many enterprises cannot immediately accept stablecoin-based settlement. Security teams may not be comfortable letting agents choose paid endpoints dynamically. We also still need more evidence that agents make better purchase and tool-selection decisions than carefully designed software.
Even with those caveats, this announcement matters because a cloud platform is treating payments as an agent primitive. AgentCore already groups runtime, gateway, identity, memory, observability, and evaluation. Adding payments expands what an agent can do in the external world.
Sending email, creating issues, editing code, and restarting servers are already meaningful actions. Spending money sits on a different accountability layer. Who approved the spend? Under what conditions? Why did the agent choose that service? Was there a cheaper alternative? Who takes the loss if the paid result is wrong or missing?
Over the last few months, the AI agent race has been shifting from model performance to runtime control. Coding agents compete on planning, diffs, approvals, hooks, MCP, sandboxing, and observability. Enterprise agent platforms compete on identity, policy, gateway, evaluation, and trace. AgentCore Payments adds spending authority to that runtime contest.
The practical next step is not to add x402 to every API tomorrow. For API builders, it is to ask whether the product can be sold as a resource an agent can understand: clear capability, clear unit of use, machine-readable price, reliable fulfillment, and abuse controls. For AI product teams, it is to decide when an agent should be allowed to spend, how much, on which resources, and under what audit trail.
AgentCore Payments is still a preview. x402 still needs ecosystem adoption and security hardening. But the direction is clear. Agents are moving from reading, writing, and calling the internet to paying for parts of it. In that world, the most important wallet feature may not be the button that opens it. It may be the rules that close it.